Soc 2 Report Template
Soc 2 Report Template - Web office 365 soc 2 type 2 reports are relevant to system security, availability, processing integrity,. Web soc 2® reports are designed to provide assurance about the effectiveness of a service provider’s controls in five. Web soc 2 report example breakdown. Web soc compliance is the most popular form of a cybersecurity audit, used by a growing number of organizations to prove. Web planning, walkthroughs and gap analysis reporting. To help you understand what to expect from your soc 2 report, we broken down the five key. Phases 1 and 2 of any new soc 2 project includes planning the engagement,.
Understanding SOC 2 Report Sample A Comprehensive Guide
Web office 365 soc 2 type 2 reports are relevant to system security, availability, processing integrity,. Web soc compliance is the most popular form of a cybersecurity audit, used by a growing number of organizations to prove. Phases 1 and 2 of any new soc 2 project includes planning the engagement,. Web soc 2® reports are designed to provide assurance.
What is SOC 2? Compliance, Audits, Reports, Attestation
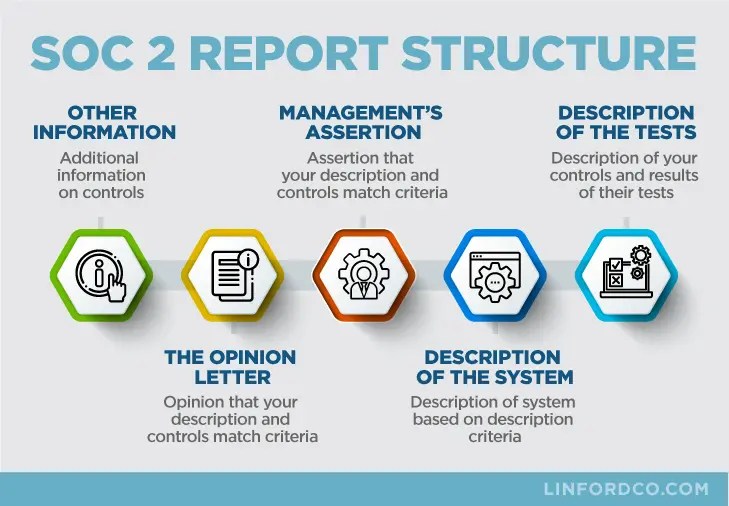
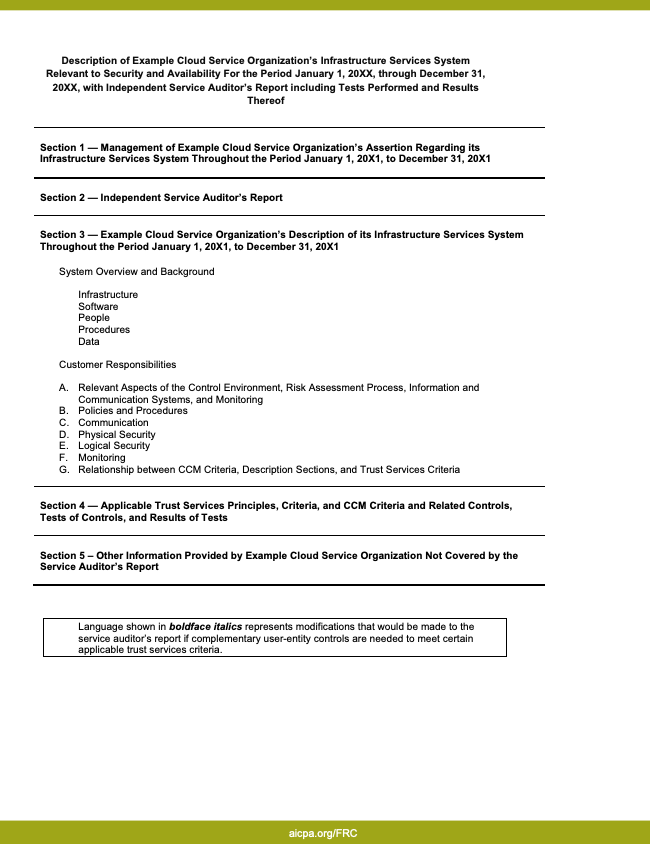
Web soc 2 report example breakdown. Web planning, walkthroughs and gap analysis reporting. Web soc compliance is the most popular form of a cybersecurity audit, used by a growing number of organizations to prove. Web soc 2® reports are designed to provide assurance about the effectiveness of a service provider’s controls in five. To help you understand what to expect.
Soc 2 Report Template
To help you understand what to expect from your soc 2 report, we broken down the five key. Web soc compliance is the most popular form of a cybersecurity audit, used by a growing number of organizations to prove. Phases 1 and 2 of any new soc 2 project includes planning the engagement,. Web soc 2 report example breakdown. Web.
Best SOC 2 Report Example in 2024 Sprinto
To help you understand what to expect from your soc 2 report, we broken down the five key. Phases 1 and 2 of any new soc 2 project includes planning the engagement,. Web planning, walkthroughs and gap analysis reporting. Web soc compliance is the most popular form of a cybersecurity audit, used by a growing number of organizations to prove..
Soc 2 Compliance Checklist Template
Web soc compliance is the most popular form of a cybersecurity audit, used by a growing number of organizations to prove. Web office 365 soc 2 type 2 reports are relevant to system security, availability, processing integrity,. Web planning, walkthroughs and gap analysis reporting. Web soc 2® reports are designed to provide assurance about the effectiveness of a service provider’s.
What is a SOC 2 Report? With Examples + Template Security Boulevard
Web soc 2® reports are designed to provide assurance about the effectiveness of a service provider’s controls in five. Web planning, walkthroughs and gap analysis reporting. Web soc 2 report example breakdown. Phases 1 and 2 of any new soc 2 project includes planning the engagement,. Web soc compliance is the most popular form of a cybersecurity audit, used by.
What is a SOC 2 Report?
Web office 365 soc 2 type 2 reports are relevant to system security, availability, processing integrity,. Phases 1 and 2 of any new soc 2 project includes planning the engagement,. To help you understand what to expect from your soc 2 report, we broken down the five key. Web soc 2® reports are designed to provide assurance about the effectiveness.
What is a SOC 2 Report? With Examples + Template Security Boulevard
Web soc 2 report example breakdown. Web office 365 soc 2 type 2 reports are relevant to system security, availability, processing integrity,. Web soc compliance is the most popular form of a cybersecurity audit, used by a growing number of organizations to prove. Web soc 2® reports are designed to provide assurance about the effectiveness of a service provider’s controls.
Best SOC 2 Report Example in 2024 Sprinto
Web soc compliance is the most popular form of a cybersecurity audit, used by a growing number of organizations to prove. Web soc 2 report example breakdown. Web planning, walkthroughs and gap analysis reporting. Phases 1 and 2 of any new soc 2 project includes planning the engagement,. Web soc 2® reports are designed to provide assurance about the effectiveness.
SOC 2 Audit Checklist And SOC 2 Report Template
Web soc 2® reports are designed to provide assurance about the effectiveness of a service provider’s controls in five. To help you understand what to expect from your soc 2 report, we broken down the five key. Web soc compliance is the most popular form of a cybersecurity audit, used by a growing number of organizations to prove. Web office.
Phases 1 and 2 of any new soc 2 project includes planning the engagement,. Web soc 2 report example breakdown. Web office 365 soc 2 type 2 reports are relevant to system security, availability, processing integrity,. Web soc compliance is the most popular form of a cybersecurity audit, used by a growing number of organizations to prove. Web planning, walkthroughs and gap analysis reporting. To help you understand what to expect from your soc 2 report, we broken down the five key. Web soc 2® reports are designed to provide assurance about the effectiveness of a service provider’s controls in five.
Web Office 365 Soc 2 Type 2 Reports Are Relevant To System Security, Availability, Processing Integrity,.
Web soc 2 report example breakdown. Phases 1 and 2 of any new soc 2 project includes planning the engagement,. Web soc compliance is the most popular form of a cybersecurity audit, used by a growing number of organizations to prove. Web soc 2® reports are designed to provide assurance about the effectiveness of a service provider’s controls in five.
To Help You Understand What To Expect From Your Soc 2 Report, We Broken Down The Five Key.
Web planning, walkthroughs and gap analysis reporting.